Providing Secure, Scalable and more Resilient Critical Infrastructures
Request a Demo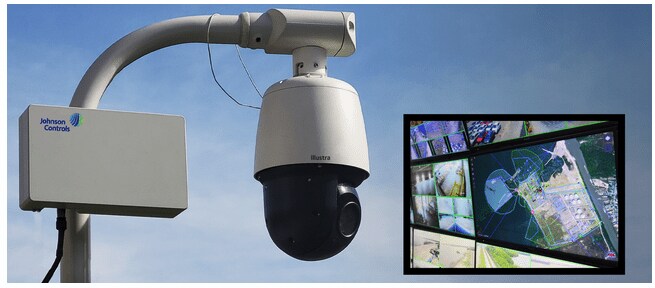
Johnson Controls and Critical Infrastructure
Johnson Controls provides technology solutions that improve employee and user satisfaction, enhance security, and overall increase functionality of the critical infrastructure. Through such security features, critical infrastructures remain secure and monitored.
Our Solutions
- Access Control
- Video Surveillance
- Intrusion
- Unified Platform
Access Control
Access controls’ real-time identity management, readers, and credentials allow for critical infrastructures to track who enters and exits buildings and grounds, monitoring through which door they entered and where they are currently located.

Video Surveillance
Johnson Controls’ video surveillance provides infrastructures with immediate visual certification of all critical locations from one command center. We help surveillance operators maintain secure facilities, effectively identify suspicious behavior, and ensure building security.

Intrusion
Identifying potential physical threats at the earliest contributes to safeguarding critical infrastructures’ integral assets, quickly alerting the right authorities, and preventing any untoward incident from occurring. Our intrusion detection offers real-time alerts, enabling a faster response to mitigate risk.

Unified Platform
Johnson Controls' unified platform provides access control, video surveillance, and intrusion features to be controlled from one centralized platform, providing true situational awareness of all events occurring in the facility.

Critical Infrastructure Challenges

Perimeter Protection
Energy, oil and gas, telecom and other critical infrastructures involve bulk power systems and significant acreage. Perimeter radar detection secures and covers the entire facility. In addition, facility lock down ensures safety among critical infrastructures, providing automatic alerts and alarms if an incident occurs.

Visibility
Critical Infrastructures often include expansive layouts that make it difficult to have visibility across all events. Johnson Controls leverages automatic processes which drives pre-designed actions and reactions to security events. Body worn cameras and AI/analytics integrate with these automatic processes giving your critical infrastructure the best possible visibility.

Visitor Management
Johnson Controls provides first-class security for industrial settings to monitor loitering, disruptive behavior and visitors. Our keyless entry limits unwanted visitors from entering more secure areas and supplies tracking and analytics on both entrances and exits.

Regulatory Requirements
Critical Infrastructures require up-to-date regulatory requirements to enhance safety on the base. However, such regulations require advanced security. With Johnson Controls' robust command center either on or off site, we help facilities maintain regulatory requirements and navigate high-stake audits.

Enhanced Cyber Standards
Johnson Controls' solutions provide facilities with the maximum-security measures needed. Our products meet the approval of our dedicated cyber protection team, formed by more than 250 engineers specialized in detecting and mitigating cybersecurity risks.

Business Continuity
Business continuity is vital to control within critical infrastructures, so Johnson Controls provides systems such as edge-recording, back-fill for cameras, and redundant application servers to maintain live situational awareness.
Why Johnson Controls?
Johnson Controls has been the leader in commercial video surveillance for 50+ years. With our comprehensive portfolio of brands designed to fit the needs of a business with one location or thousands of locations, we can help design your ideal security solution.

Ask us a Question

Compliance and Cybersecurity
Johnson Controls designs cybersecurity into our product and solution offerings and endeavors to protect those solutions (including software, hardware and hosted services) to secure your data and operations across the risk management lifecycle. Our secure product practices include the design, sourcing, development, deployment, servicing, support and retirement of products. All new Johnson Controls commercial products are developed under governance of our cybersecurity policies, standards and guidelines, which includes requirements for product testing and vulnerability management.
Critical Solutions for Critical Infrastructures
• Real Time Situation Awareness with Video Integration
• Perimeter Protection with the Latest in Radar Technology
• Multi-factor Authentication
• Automatic Audit Reporting
• Mustering
• Mass Notification


Interested in learning more?
Download Brochure


